Mobile platforms are maturing as technology advances, with smartphones and tablets now performing like the traditional desktop computers, an advancement that is making it easier for criminals to build malware for the devices.
Also contributing to the increasing cases of malware presence is the growing use of mobile apps, where users download the apps without carefully considering the security needed. This is according to the Cisco 2014 Annual Security Report.
According to the report, the bring-your-own-device (BYOD) trend being advocated by technology companies around the world is complicating efforts by security teams to secure users accessing applications from their devices.
Cisco says that security teams are facing the challenge of managing these devices, especially because they have to work on a limited IT budget.
Criminals have found new ways to compromise users and data due to growing mobility by using wireless channels to eavesdrop and gain access to information being exchanged through the channels, with organizations losing intellectual property in the case an employee’s device is lost or stolen.
In order to deal with these challenges, Cisco experts propose that organisations should come up with a formal program for managing mobile devices in efforts to help ensure that all devices are secure before accessing the network.
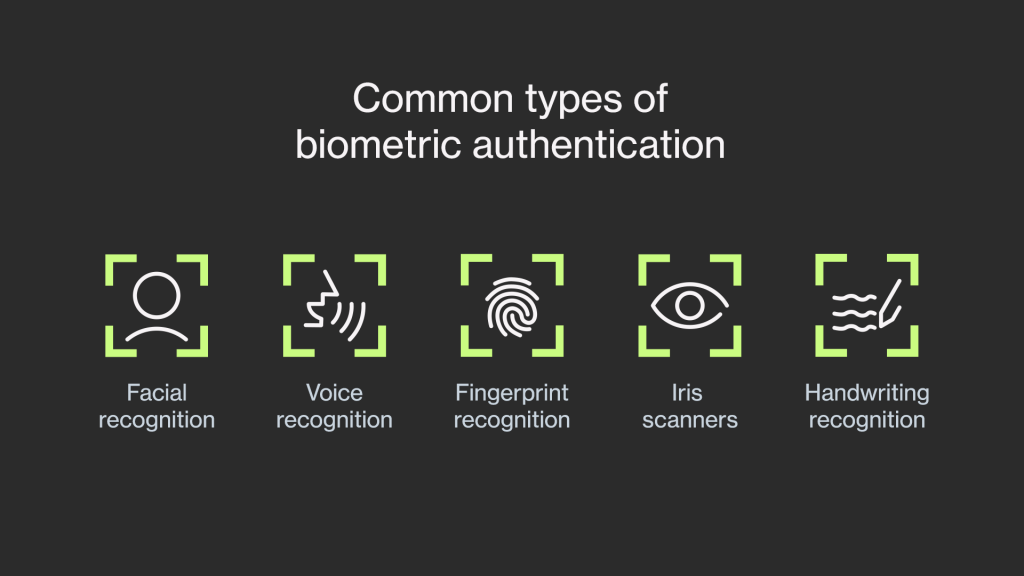
Also, enterprises should implement user authentication through the use of a Personal Identification Number (PIN) with security teams being able to turn off or wipe clean the device remotely if it is reported lost.
Mobile malware is reportedly common among Android devices, with 99 per cent of all intended malware targeting devices that run on Google’s range of Android platforms.
According to an analysis carried out by Cisco researchers last year, Android users have the highest encounter rates with all forms of web-delivered malware at 71%, with Apple iPhone users following behind at 14%.
The Cloud Services
Another growing security concern addressed in the report is the ever increasing use of the cloud by enterprises to store large amounts of critical business data.
With the cloud network traffic predicted to grow more than threefold by 2017, organizations will expect to lose the ability to see who and what is moving in and out of corporate boundaries, and what actions users are taking.
This transition to the cloud is expected to change operations completely as it redefines where data is stored, moved and accessed creating numerous opportunities for attackers.
“Today the radical shift comes from the cloud,” comments Michael Fuhrman, Vice President of engineering at Cisco. “Not only do businesses hold most of their critical applications in the cloud, but they are also using the cloud to consume and analyse critical business information”.
The report cites lack of information about how cloud vendors defend their products against security breaches as a big risk, since organisations do not ask enough questions about what is contained in their vendors’ service agreement or how often the security software is upgraded.
Cisco 2014 security survey also found out that cybercriminals are now widely targeting the internet infrastructure which they have realised provides better benefits than individual computers, with a new focus in web hosting servers, name servers and data centres so as to take advantage of their bandwidth.
“Cybercrime has become so lucrative and heavily commoditized that it needs more powerful infrastructure to keep it afloat,” said Gavin Reid, director of threat intelligence at Cisco.
“By compromising hosting servers and data centres, attackers gain not only access to large amount of bandwidth but also the benefit of continuous uptime for those resources.”
As online criminals continue to exploit users in consumer application and devices, Cisco says the use of traditional security that involves layering of products and use of multiple filters is not enough to curb the latest generation malware.
Organisations should incorporate real-time threat intelligence based on the cloud, such as the Cisco Security Intelligence Operations (SIO), a hub that aims to protect data in a time when Cloud computing, BYOD and massive distributed networking are taking over other technologies.